1 min read
3 Ways to Prep for Your High-Reliability Class 3 Electronics Project
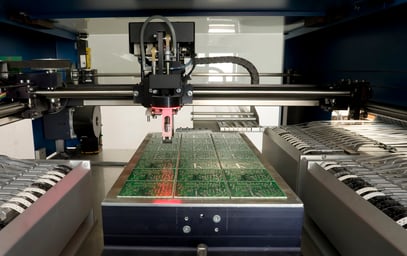
You’re an original equipment manufacturer (OEM) in need of an electronics contract manufacturer (ECM) to supply circuit boards for a product you...
3 min read
 Matric Group
:
Updated on December 19, 2024
Matric Group
:
Updated on December 19, 2024

 You probably take plenty of steps to protect intellectual property at your OEM. But what about the other guys handling your sensitive secrets?
You probably take plenty of steps to protect intellectual property at your OEM. But what about the other guys handling your sensitive secrets?
For many projects, one of the most important factors in choosing an electronics contract manufacturer is how it handles intellectual property (IP). The manufacturing plant security procedures your contractor enforces -- both physical and digital -- say a lot about the company’s commitment to customer success.
Here’s how and why a well-run electronics contract manufacturer (ECM) should address your concerns.
Electronics are evolving at warp speed -- it’s no longer a shock to see something become obsolete in under 2 years. You and your competitors sink huge chunks of cash into R&D to make better, faster iterations at an increasingly rapid pace.
You put a lot into your IP. The consequences of a leaked patent or electronics design could be devastating, especially in sensitive industries like military & defense.
Properly developed standards assure the customer that its ideas are in capable hands.
Has your contract electronics manufacturer taken every possible measure to ensure product and data safety? If not, don’t be shocked when an aggressive competitor -- or country -- swoops in and you don’t have that crucial digital IP to yourself anymore.

An electronics contract manufacturer that specializes in IP protection is a step above its competitors because so much of the information you provide to it is proprietary. If a potential partner doesn’t have manufacturing security standards in place, it should be a conversation-ender. If the manufacturer does have practices and they aren’t airtight, you could be in big trouble.
Cybersecurity in manufacturing should include a proven change control process. The ECM should make zero changes to your IP without approval. In other words, the contractor can’t tweak the design to make its job easier without collaborating with you.
A great way to gauge an electronics contractor’s intellectual property security efforts is to see it in person. An on-site look at how the manufacturer does business can be eye-opening:
For more information on Matric's capabilities, check out our capabilities and service guide below:
To further illustrate how secure your IP should be, consider the exhaustive steps we take to ensure IP safety throughout all stages of development.
When you’re making that in-person visit, you should watch for additional on-site, physical procedures like those at Matric/Dynamic:
Since hackers and secret-stealers are always upping their game, it’s on your electronic manufacturing services provider to keep evolving, too.
Here are a few of the ways we do that:
We are constantly researching, implementing, and updating processes to keep your information safe and secure.
If you’re a Class 2 or Class 3 electronics maker with a sensitive project, scope out your potential partners’ security standards. Not only should your ECM have perfected its information security standards, but it also should be staying ahead of future challenges.
If you have additional questions about the range of services and capabilities an ECM should offer, grab the free download below:
(Editors Note: This article was originally published in November 2019 and was updated in September 2021 to reflect industry changes and new information.)

1 min read
You’re an original equipment manufacturer (OEM) in need of an electronics contract manufacturer (ECM) to supply circuit boards for a product you...

1 min read
You’ve heard about the many great feats and discoveries in the aerospace industry. You’ve also heard about the tragedies that have happened when a...

1 min read
Understanding your marketing is key to a successful product run. That applies not only to your customers, but their home country as well.