1 min read
Tariffs on Electronics From China: Another Delay
If there's anything certain in the U.S.-China tariffs staredown, it's uncertainty.
3 min read
 Matric Group
:
Updated on December 19, 2024
Matric Group
:
Updated on December 19, 2024
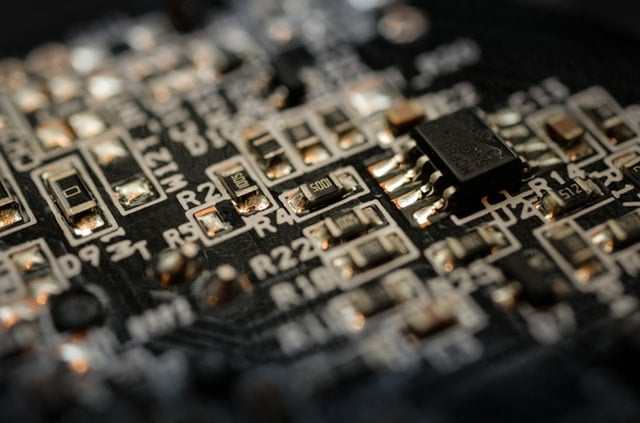
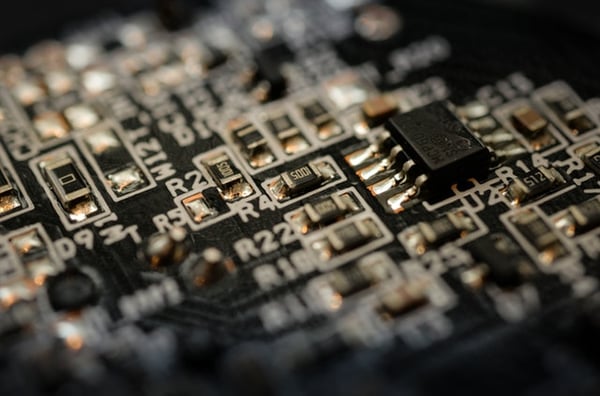 On Oct. 4, a story by Bloomberg that detailed allegations of China’s military infiltration into servers used by about 30 U.S. companies and top government agencies sent shockwaves across the tech industry. According to Bloomberg, Chinese spies sneaked tiny microchips capable of editing code from a remote location into motherboards of servers made by the world’s leading server maker – Super Micro Computer, commonly referred to as Supermicro.
On Oct. 4, a story by Bloomberg that detailed allegations of China’s military infiltration into servers used by about 30 U.S. companies and top government agencies sent shockwaves across the tech industry. According to Bloomberg, Chinese spies sneaked tiny microchips capable of editing code from a remote location into motherboards of servers made by the world’s leading server maker – Super Micro Computer, commonly referred to as Supermicro.
OEM electronics manufacturers are probably wondering whether China spying with a microchip could affect their business.
The answer: Yes! Without a doubt, it’s a huge problem for the whole global supply chain industry, and U.S.-based vendors will have to rethink about their supply chain options and security -- and whether reshoring is a viable option.
Never heard about Supermicro? It’s one of the biggest tech companies in the U.S., based in San Jose, Calif. It has a massive global network of manufacturing operations -- with China being its most preferred location for the manufacturing of motherboards. These motherboards are relied upon by thousands of companies in the tech industry, both directly and indirectly.
Amazon is one of the giant companies that depend on them for its data center servers, which power Apple’s iCloud and the Amazon Web Services. Apple was also a huge customer of Supermicro and had planned to order over 30,000 servers for a global network of its data centers before severing ties with the manufacturer in 2016 for “unrelated reasons.”
Through a top-secret probe, investigators found out that the small chips – almost the size of a grain of rice – allowed attackers to create a backdoor into any network that included the affected machines. They also established that the microchips had been inserted on the affected motherboards during their assembly by manufacturing contractors in China. Considering the magnitude of motherboards and related equipment likely to be affected by this attack, the repercussions could be massive and devastating for companies and government agencies across the world.
According to Bloomberg, one government official stated that China’s goal is to gain long-term access to sensitive government networks and high-value corporate secrets. This comes at a time when U.S. President Donald Trump has introduced tariffs on Chinese goods so that OEM electronics manufacturers will stop manufacturing their products in China.
Apple, Amazon, and Supermicro have since issued detailed reports denying any penetration into their equipment and networks. However, even if the story proves to be false, it’s an eye-opener. Considering it’s only the latest of its kind, there could certainly be more to come.
To recap the digital battle:
Industry executives have warned that the Chinese microchip attack brought to light serious vulnerabilities in the supply chain process for OEM electronics manufacturers.
When your manufacturing process is hacked or interfered with, it raises extreme concerns about the security of your whole supply chain. Companies have long considered supply chain attacks as a major risk factor in outsourcing manufacturing components, particularly from nations such as China. Just check out the way Apple, Amazon, and Supermicro shares dipped after the Bloomberg story.
However, the real dilemma for OEM electronics manufacturers sourcing parts from China is that many can’t pull out now because it’ll cost them more to make their products in their home country. Labor, assembly, and expertise in China are cheaper than anywhere else in the world. No wonder over 75% of the world’s mobile phones and 90% of PCs come from China.
“But my company is nowhere close to Apply’s size and scope,” you might be saying. It’s true that the Chinese probably aren’t spying on your company -- no offense, but you probably don’t have much top-secret info they’re after. But a hack of this nature should still sound an alarm for most companies, no matter the size.
So, the big question for OEM electronics companies now will be how to secure their hardware supply chain tighter than ever.
The best thing you do to secure your supply chain is buy only from verified, trustworthy sources.
Even still, a dependable outsourcing doesn’t guarantee you 100% safety -- nothing ever will. Supermicro is the biggest company in the world in this market, and they’re pretty reliable in most people’s minds. Unfortunately, in this case they weren’t.
Even if you’re a small- or mid-sized OEM company that uses electronic components, the fact that you’re vulnerable to a microchip or similar attack means it’s worth tightening security. This attack should especially be a red flag for companies who work in government or defense fields.
So close up your circle of trust and keep on the lookout for similar news stories in the future!

1 min read
If there's anything certain in the U.S.-China tariffs staredown, it's uncertainty.
.jpg)
1 min read
NOTE: This article was updated on July 3, 2025 to reflect recent information regarding tariffs.

1 min read
The electronics manufacturing supply chain is a major risk for many OEMs. Challenges in this area include environmental and global regulations, which...